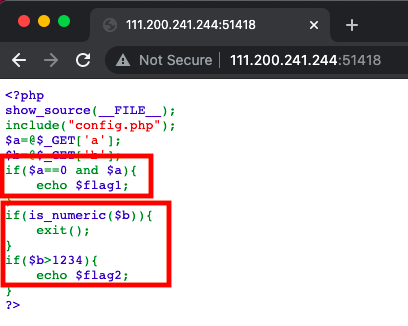
We notice taht the first condition needs us upload parameter ‘a‘ which is equal to 0 and is TRUE value.
So if the parameter ‘a‘ is 0, it represents FALSE that can not make the IF condition operation.
You know PHP is a weakly-typed language, so something like ‘0a‘ is actually equal to ‘0‘ when comparison.
And ‘0a‘ is also True value cuz it‘s not NULL string.
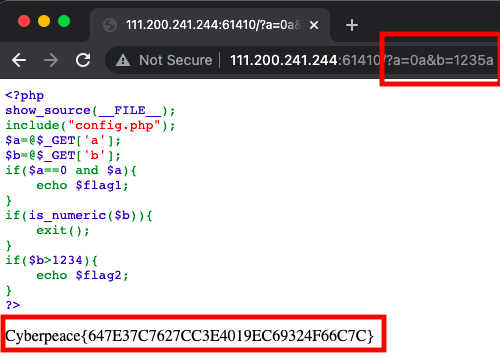
Therefore, we just construct the payload ‘a=0a‘ to bypass the first condition.
Another parameter ‘b‘ demand us upload a string not only contains numeric, we still could construct that stuff payload to bypass.
原文:https://www.cnblogs.com/4fun/p/15120967.html